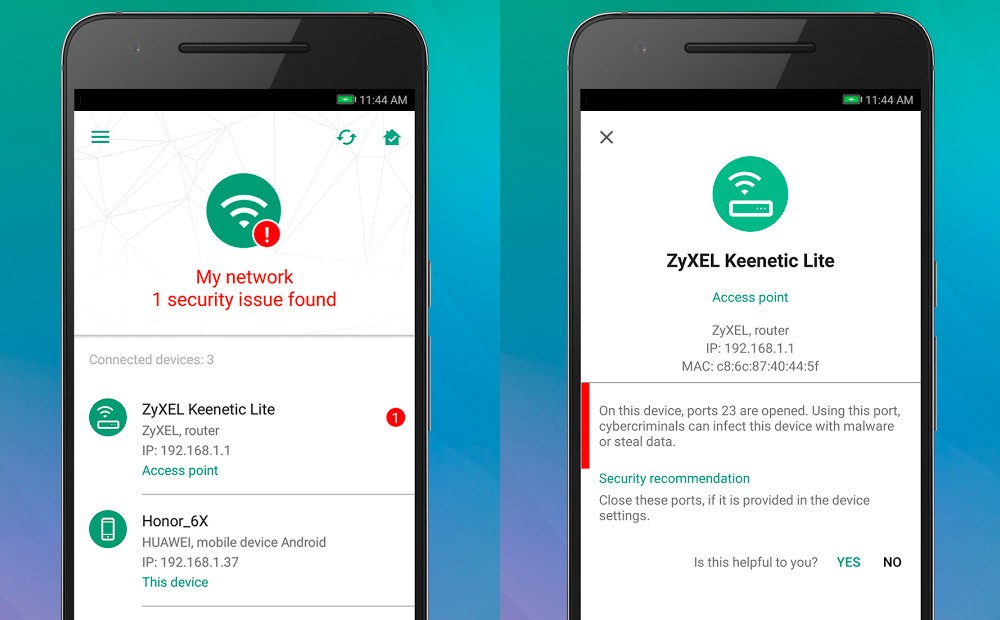
IOT-Protect-Continous-Vulnerability-Scanner/scan.py at master · billy-osullivan/IOT-Protect-Continous-Vulnerability-Scanner · GitHub
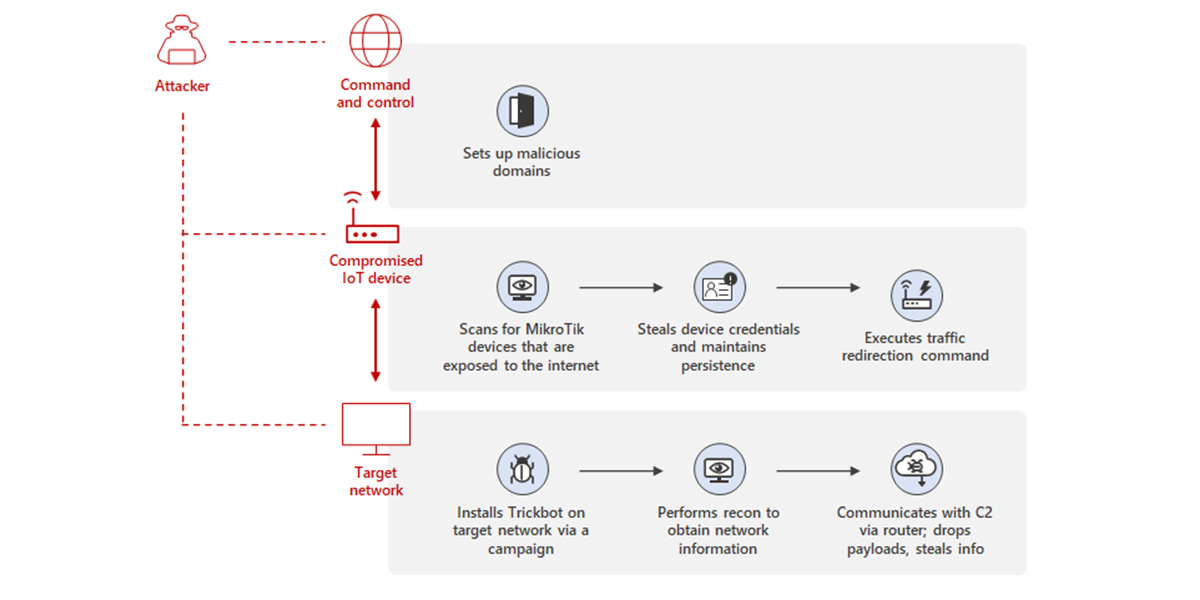
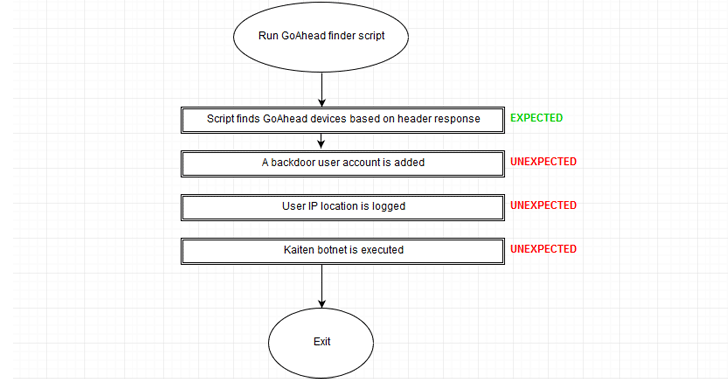
Uncovering Trickbot's use of IoT devices in command-and-control infrastructure | Microsoft Security Blog
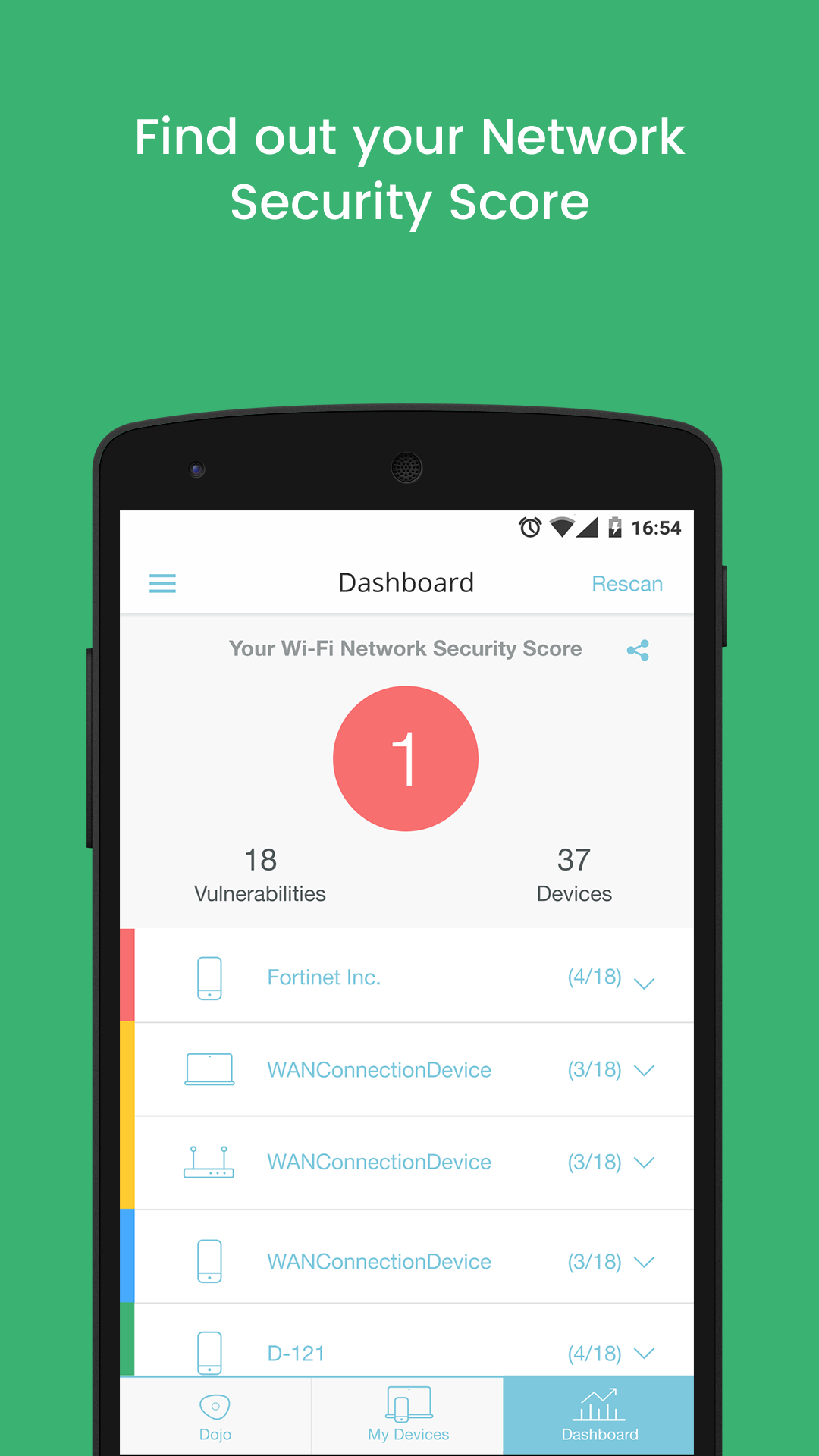
New Dojo Intelligent IoT Vulnerability Scanner App Provides Consumers With Deep Insight Into The Cybersecurity Risks In Their Smart Homes
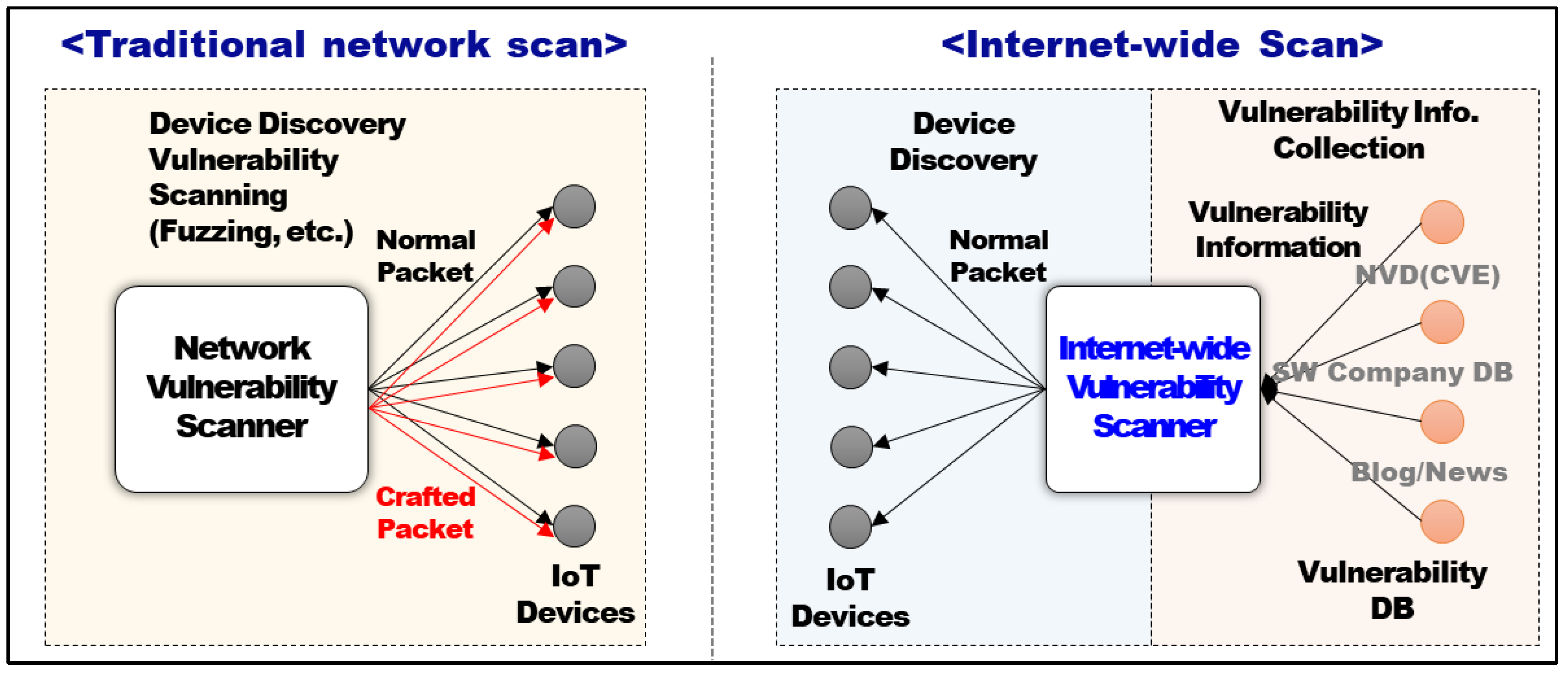
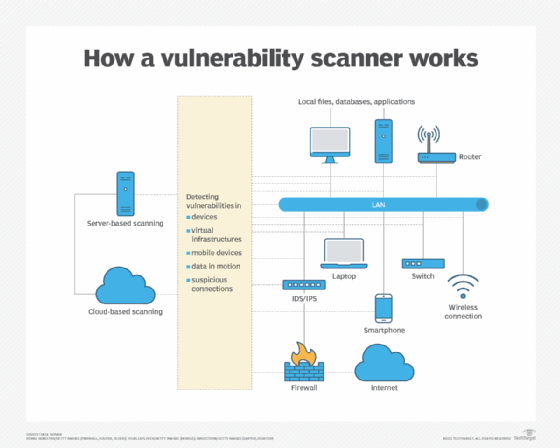
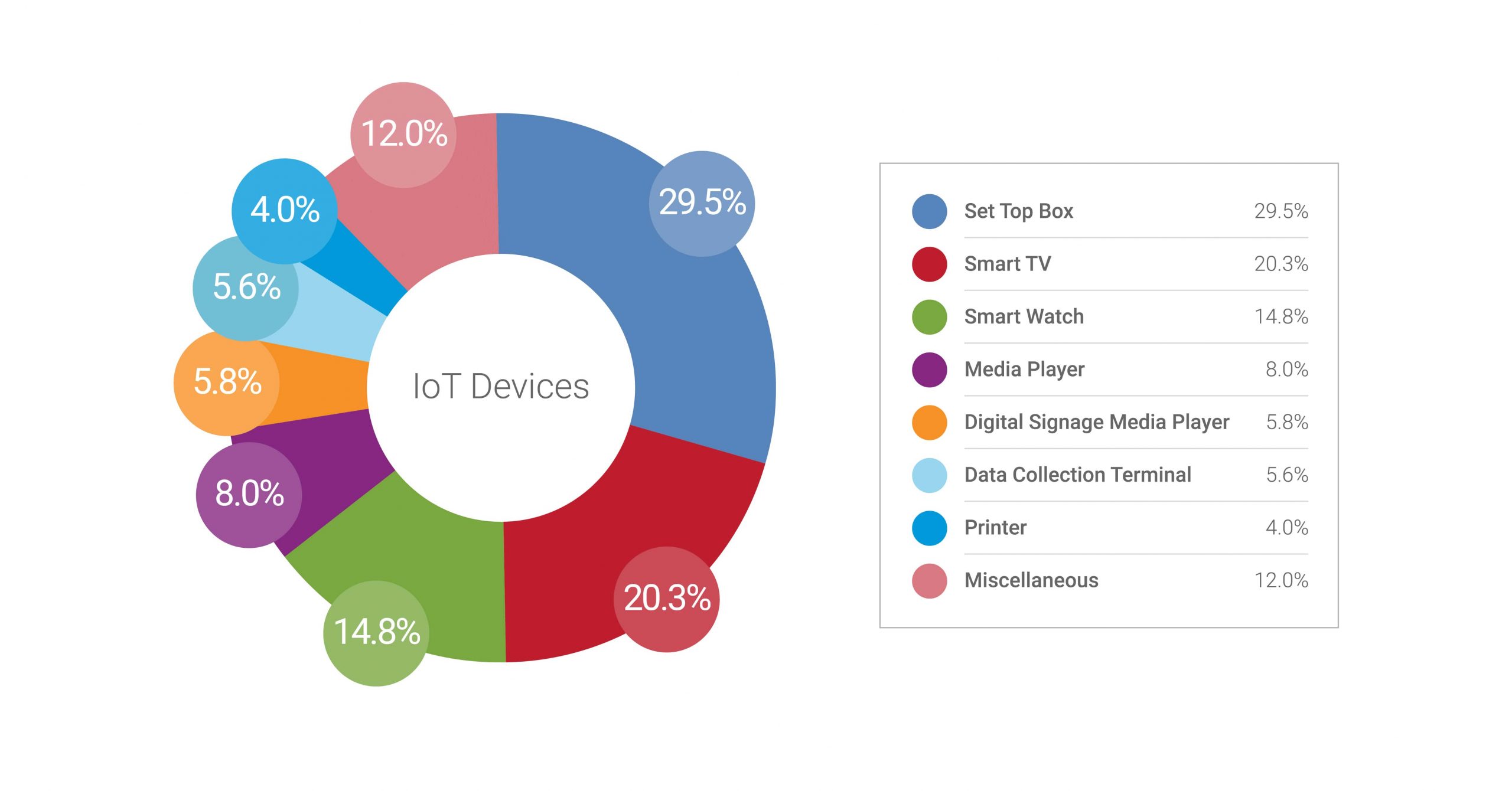
Symmetry | Free Full-Text | An Intelligent Improvement of Internet-Wide Scan Engine for Fast Discovery of Vulnerable IoT Devices

Vulnerability Scanning System Used in the Internet of Things for Intelligent Devices | Semantic Scholar
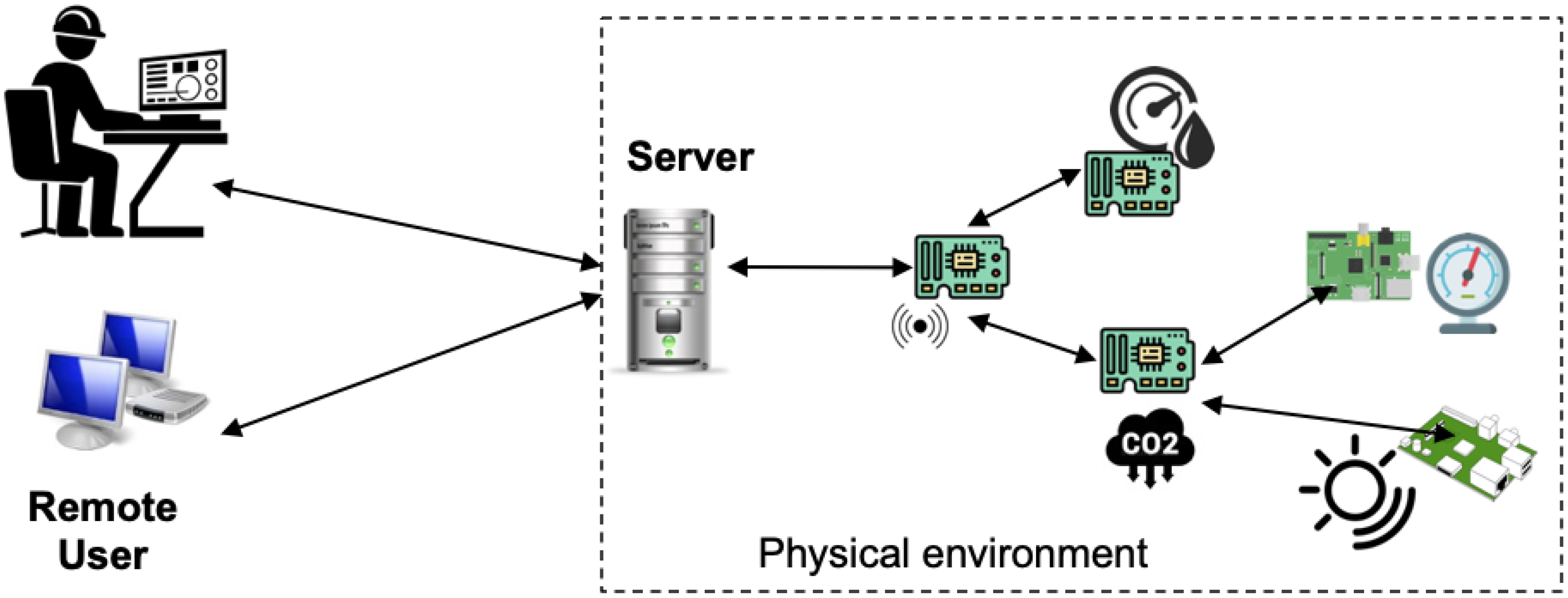
![PDF] The Forgotten I in IIoT: a vulnerability scanner for industrial internet of things | Semantic Scholar PDF] The Forgotten I in IIoT: a vulnerability scanner for industrial internet of things | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/135adee53b8f22156bba4bb774745e1ddc742357/2-Figure1-1.png)
PDF] The Forgotten I in IIoT: a vulnerability scanner for industrial internet of things | Semantic Scholar

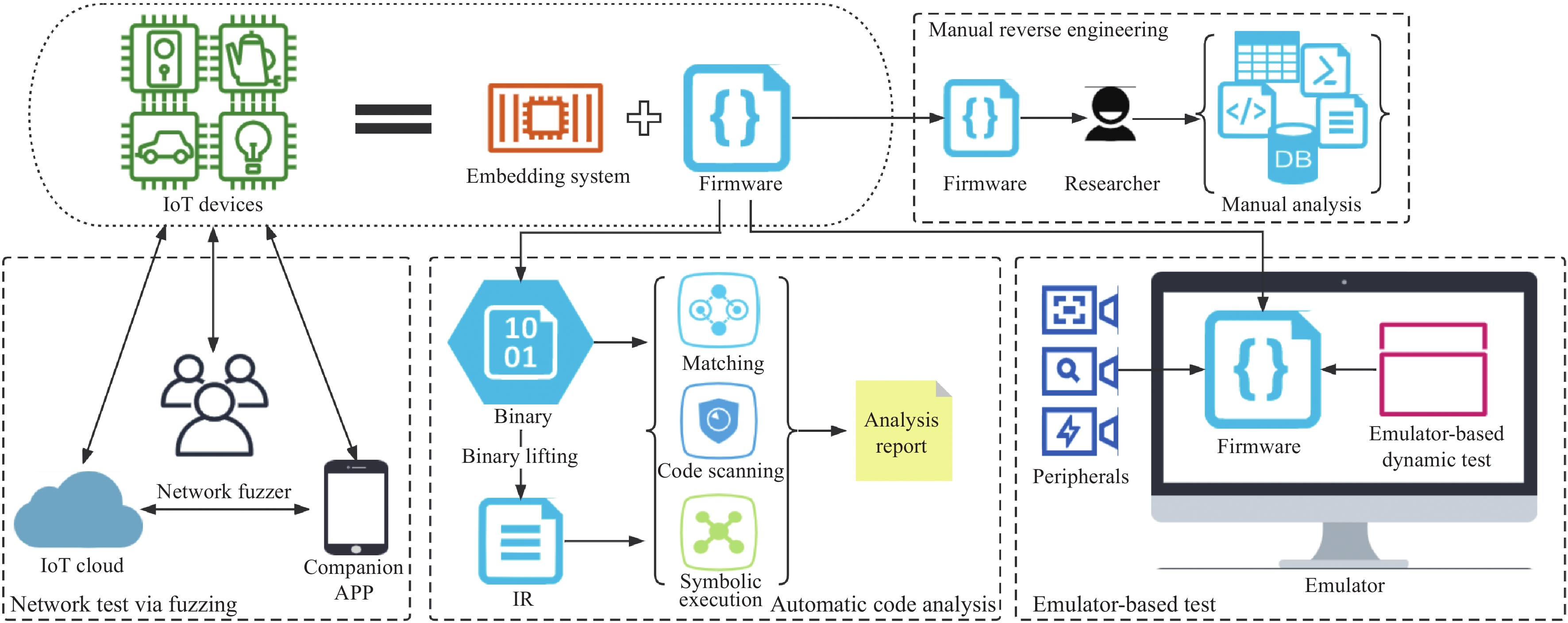
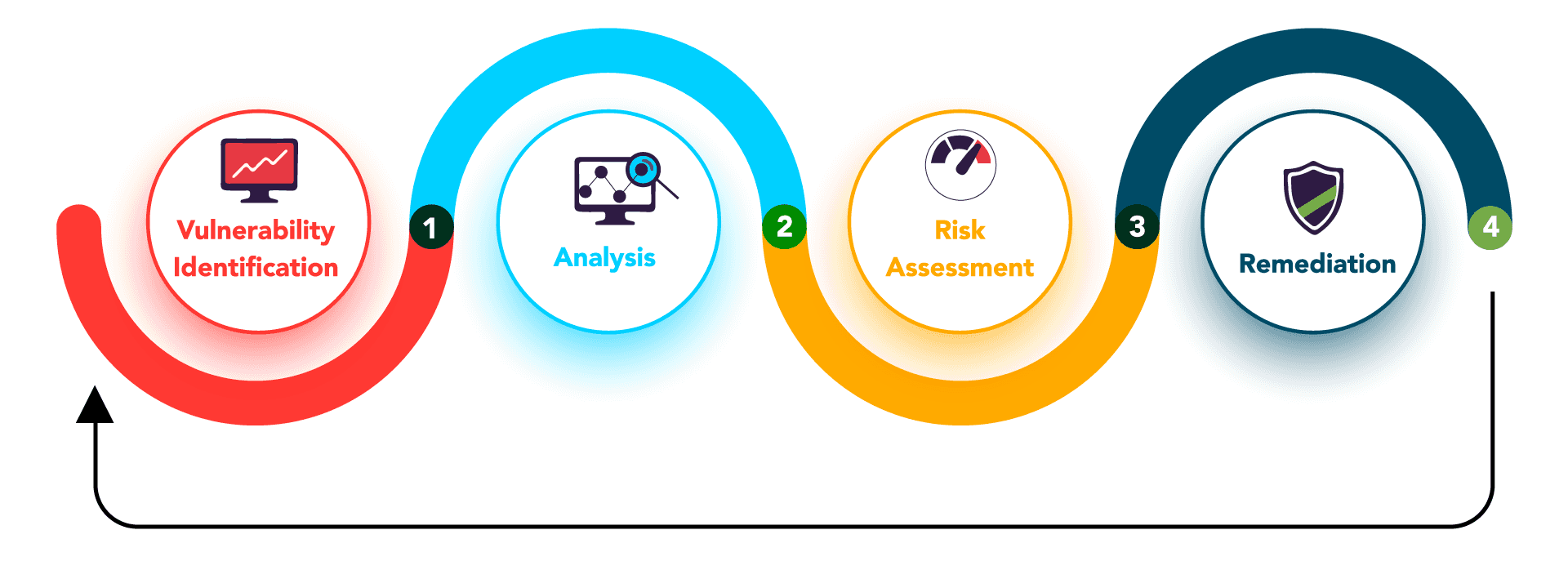
A survey on IoT & embedded device firmware security: architecture, extraction techniques, and vulnerability analysis frameworks | Discover Internet of Things

Microsoft's new security tool will discover firmware vulnerabilities, and more, in PCs and IoT devices | TechRepublic
Sensors | Free Full-Text | Improving Security of Web Servers in Critical IoT Systems through Self-Monitoring of Vulnerabilities
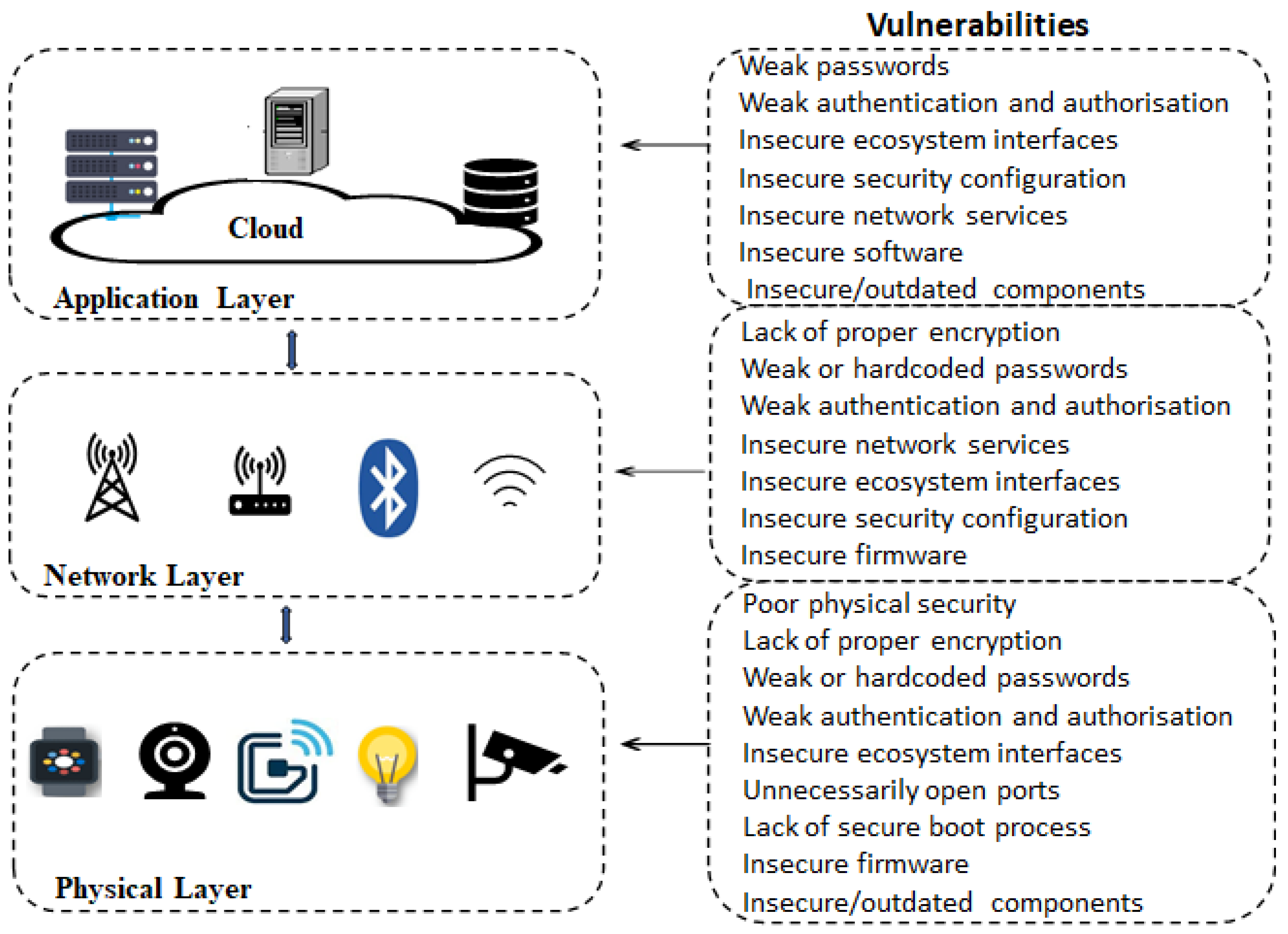
Electronics | Free Full-Text | Analysis of Consumer IoT Device Vulnerability Quantification Frameworks

![5 Challenges of IoT Security and Tips to Secure Your Devices [Infographic] - SecurityHQ 5 Challenges of IoT Security and Tips to Secure Your Devices [Infographic] - SecurityHQ](https://www.securityhq.com/wp-content/uploads/2023/11/SecurityHQ-Infographic-5-Challenges-of-IoT-Security-and-Tips-to-Secure-Your-Devices.jpg)