James Kettle on X: "Backslash Powered Scanner now uses the 'COM1' Windows reserved filename to identify if your input is being used in a file path on a backend. Also, you can
False positives/bad higlighting scanning REST url paths · Issue #2 · PortSwigger/backslash-powered-scanner · GitHub
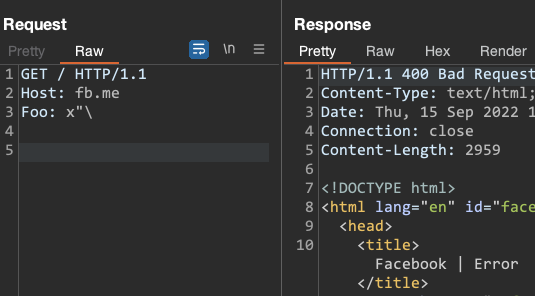
James Kettle on X: "Facebook's servers give a mystery error if you send any HTTP header that contains " and ends in \. But not if you omit the " or the \

James Kettle on X: "How are people finding this - has it found anything juicy for you? Any common cases where it flags something that isn't really iterable?" / X